Supermicro 安全中心是 Supermicro 提供產品安全更新與資訊的既定來源,Supermicro 是企業運算、儲存、網路和綠色運算技術的全球領導者。我們致力於持續改進我們的安全實務。
客戶的安全是我們的首要任務;因此,我們已採取措施來保護您的 Supermicro 伺服器和儲存系統的運作。當今的伺服器和儲存系統變得更加多功能,但也更加複雜,需要加以保護。面對威脅行為者,Supermicro 正在開發防禦機制,以保護使用者和客戶,從而將我們的安全知識提升到業界最高水準。Supermicro 認識到客戶期望部署符合高安全標準的產品;因此,我們的應對措施旨在提供最高等級的保護。
Supermicro 建議您遵循安全最佳實務,包括保持作業系統更新,並執行最新版本的韌體和所有軟體。
生命週期網路安全產品保護
Supermicro 提供三款完全在美國製造的伺服器產品。透過將製造集中在美國工廠,可確保系統的完整性。這些「美國製造」產品減少了外國網路安全入侵的機會,並可供全球客戶使用。若要深入了解此計畫,請前往美國製造解決方案頁面。
Supermicro 在整個供應鏈系統中嚴格管理網路安全實務,採用更廣泛的「從搖籃到墳墓」方法,確保我們的產品從採購、生產、營運到自然生命週期結束的整個過程都安全無虞。
Supermicro 的最佳實務旨在滿足其產品安全要求,這些要求由豐富的安全功能和特性支援。這些功能確保客戶 Supermicro 的產品符合業界安全標準。
最後更新日期:
Supermicro 極為Supermicro 您的資料中心安全。Supermicro 針對新推出的 X14/H14 以及 X13/H13/R13 以及 X12/H12 系列伺服器與儲存系統。這些內建功能將作為您在資料中心內建立安全運作的指引。請參閱以下清單。
| 類別 | 安全規範 | IntelX14 | AMD H14 | IntelX13 | AMD H13 | Ampere 產品1 | IntelX12 | AMD H12 |
|---|---|---|---|---|---|---|---|---|
| 硬體 | 矽根信任 | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ |
| 底盤入侵防護 | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | |
| 可信平台模組 (TPM) 2.0 | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ||
| BMCTPM1 | ✔ | ✔ | ✔ | ✔ | ||||
| 英特爾開機防護 | ✔ | ✔ | ✔ | |||||
| Intel® 軟體防護擴充功能(Intel® SGX)1 | ✔ | ✔ | ✔ | |||||
| AMD 處理器 | ✔ | ✔ | ✔ | |||||
| AMD 記憶體加密 (SME) | ✔ | ✔ | ✔ | |||||
| AMD 加密虛擬化 (SEV) | ✔ | ✔ | ✔ | |||||
| BIOS/BMC | 安全啟動 | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ |
| 安全磁碟清除 | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | |
| 安全快閃記憶體 | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | |
| 安全的韌體更新 | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | |
| 加密簽署的韌體 | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | |
| 安全Redfish API3 | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | |
| 密碼安全 | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | |
| USB動態啟用/停用 | ✔ | ✔ | ||||||
| 硬碟密碼 | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | |
| BMC 唯一密碼 | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | |
| 自動韌體恢復 | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | |
| 反回滾 | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ||
| 執行階段 BMC 防護機制 | ✔ | ✔ | ✔ | ✔ | ||||
| 系統鎖定 | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ||
| 供應鏈安全:遠端驗證 | ✔ | ✔ | ✔ | ✔ | ||||
| 驅動金鑰管理(超級守護者) | ✔ | ✔ | ✔ | ✔ | ✔ | |||
| IPMI 2.0 使用者鎖定 | ✔ | ✔ | ✔ | ✔ | ✔ | |||
| 安全狀態監控 | ✔ | ✔ | ✔ | ✔ | ||||
| 安全協議與資料模型(SPDM)管理2 | ✔ | ✔ | ✔ | ✔ | ||||
| 標準 | 美國國家標準與技術研究院特別出版物 800-193 | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | |
| 美國國家標準與技術研究院特別出版物 800-147b | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ||
| 美國國家標準與技術研究院特別出版物 800-88 | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ |
註記:
- 某些功能可能不適用於所有產品。
- 1適用於特定型號及配置
- 2計劃於2024年第四季度實施
- 3TLS v1.2 / v1.3 受支援。RMCP+ 加密套件 3 / 17 受支援。
基板管理控制器(BMC)為不同地點的多名使用者提供遠端網路存取功能。BMC使系統管理員能夠遠端監控系統健康狀態並管理電腦事件。BMC搭配智能平台管理介面(IPMI)管理工具使用,實現對伺服器的集中控制與監控。BMC具備廣泛的安全功能,可滿足客戶需求。

資料中心中啟用 BMC 功能之伺服器管理的安全最佳實踐
動態系統驗證運用驗證流程
使用系統驗證偵測硬體與韌體的任何變更
加密簽署的基礎管理模組韌體
瞭解安全性功能,以加密簽署 BMC 韌體和 BIOS
BMC 獨特密碼安全功能
瞭解如何從BMC 唯一密碼中獲益
Intel 平台更新 (IPU) 2026.2 版,2026 年 5 月
此更新適用於搭載 IntelXeon® Intel 處理器的X14 。Intel 平台更新 (IPU) 整合了先前可能分別提供的各項安全性更新。
- INTEL-SA-01420 – 2026.2 IPU - Intel® 處理器韌體安全公告
AMD 公告 AMD-SB-303AMD,2026 年 5 月
Supermicro AMD EPYC™ AMD EPYC™ 可能存在的漏洞,這些漏洞會影響AMD 處理 (ASP) 及AMD 虛擬化 – 安全嵌套分頁 (SEV-SNP) 功能;Supermicro AMD EPYC™ AMD EPYC™ 平台中可能存在的其他漏洞,這些漏洞會影響AMD (ASP) 及AMD 虛擬化 – 安全嵌套分頁 (SEV-SNP)。AMD 針對此漏洞AMD 緩解措施。此漏洞影響Supermicro H12、H13 H14 BIOS。
- CVE-2024-36315
- CVE-2025-61971
- CVE-2025-61972
Intel 平台更新 (IPU) 2026.1 更新(第 2 部分),2026 年 5 月
此更新適用於搭載 IntelXeon® Intel 處理器的X13 。Intel 平台更新 (IPU) 整合了先前可能分別提供的各項安全性更新。
- INTEL-SA-01413 – 2026.1 IPU - UEFI 參考韌體安全公告
AMD 公告AMD,2026 年 4 月
Supermicro 項安全問題,即若錯誤使用 LocateProtocol 服務,可能導致權限從 Ring 0 提升至系統管理模式 (SMM),進而可能引發任意程式碼執行。AMD 針對此漏洞AMD 緩解措施。此漏洞影響Supermicro H12、H13 及H14 BIOS。
- CVE-2025-54502
AMD 公告AMD,2026 年 4 月
Supermicro 一項安全問題,即具備特權的攻擊者可能篡改記憶體映射 I/O(MMIO)路由配置寄存器,進而可能危及 SEV-SNP 來賓系統的記憶體完整性。AMD 針對此漏洞AMD 緩解措施。此漏洞影響Supermicro H12、H13 及H14 BIOS。
- CVE-2025-54510
AMD 公告AMD,2026 年 4 月
Supermicro 一安全問題:內部安全稽核發現一項潛在漏洞,可能導致惡意虛擬化管理程式指示 IOMMU 將資料寫入 Secure Encrypted Virtualization-Secure Nested Paging (SEV-SNP) 虛擬機記憶體中。AMD 針對此漏洞AMD 緩解措施。此漏洞影響Supermicro H12、H13 及H14 BIOS。
- CVE-2023-20585
Intel 平台更新 (IPU) 2025.3 版 第 2 部分,2026 年 3 月
此更新適用於搭載 IntelXeon® Intel 處理器的X11、X12、X13 及X14 。Intel 平台更新 (IPU) 整合了先前可能分別提供的各項安全性更新。
- INTEL-SA-01234 – 2025.3 IPU - UEFI 參考韌體安全公告
AMD 公告 AMD-SB-705AMD,2026 年 2 月
Supermicro 項安全問題,該問題可能導致客體虛擬機器 (VM) 造成主機系統當機。AMD 針對此AMD 緩解措施。此漏洞影響Supermicro H11、H12、H13 及H14 BIOS。
- CVE-2023-31364
英特爾平台更新 (IPU) 更新 2026.1,2026年2月
此更新適用於搭載 IntelXeon® Intel 處理器的X11、X12、X13 及X14 。Intel 平台更新 (IPU) 整合了先前可能分別提供的各項安全性更新。
- INTEL-SA-01314 – 2025.4 IPU - Intel® TDX 模組安全公告
- INTEL-SA-01315 – 2026.1 IPU - Intel® 晶片組韌體安全公告
- INTEL-SA-01396 – 2026.1 IPU - Intel® 處理器韌體安全公告
- INTEL-SA-01397 – 2026.1 IPU - Intel® 信任域擴展 (Intel® TDX) 模組安全公告
AMD 公告AMD,2026 年 2 月
Supermicro AMD EPYC™ 存在潛在漏洞,這些漏洞影響 I/O 記憶體管理單元 (IOMMU)、AMD 虛擬化 – 安全嵌套分頁 (SEV-SNP) 以及其他平台組件,且是在內部及第三方審計過程中發現的。此漏洞影響Supermicro H11、H12、H13 及H14 BIOS。
- CVE-2025-52533、CVE-2025-29950、CVE-2024-36355、CVE-2025-29939、CVE-2025-0012、CVE-2025-52536、CVE-2024-21961、 CVE-2025-29948、CVE-2024-21953、CVE-2025-29952、CVE-2025-52534、CVE-2025-54514、CVE-2025-48517、 CVE-2025-0031、CVE-2024-36310、CVE-2025-29946、CVE-2025-48514、CVE-2025-0029、CVE-2025-48509
Microsoft 開機 CA 2011 終止支援:轉用 2023 年憑證
MicrosoftSecure Boot CA 2011 憑證將於 2026 年 6 月到期,屆時僅依賴這些憑證的裝置將無法再收到Windows 管理員和 Secure Boot 元件的安全更新,從而增加遭受開機套件攻擊的風險。Microsoft 過渡至新的 2023 年憑證;Supermicro 支援的 BIOS 更新,使用者應保持「安全開機」功能啟用、安裝最新的 BIOS/韌體,並套用所有更新——由於支援的裝置將自動進行過渡,因此多數系統無需立即採取行動。
詳細資訊Supermicro BMC 韌體漏洞,2026 年 1 月
在部分 Supermicro 主機板中已發現數個安全性問題。這些問題影響 Supermicro BMC 韌體。
- CVE-2025-12006
- CVE-2025-12007
AMD 公告AMD,2026 年 1 月
Supermicro 安全問題,即「過期 RLB 條目」(Stale RLB Entry)可能導致 Secure Nested Paging(SNP)的活躍虛擬中央處理器(vCPU)重複使用其他虛擬機器(VM)的 TLB 條目,進而可能危及資料完整性。AMD 針對此漏洞AMD 緩解措施。此漏洞影響Supermicro H12 H14 BIOS。
- CVE-2025-29943
Supermicro BMC 韌體漏洞,2025 年 11 月
在部分 Supermicro 主機板和 CMM 中已發現四個安全性問題。這些問題可能影響 Supermicro BMC 韌體。
- CVE-2025-7623
- CVE-2025-8076
- CVE-2025-8404
- CVE-2025-8727
AMD 公告AMD,2025 年 11 月
Supermicro 安全問題,即「過期 RLB 條目」(Stale RLB Entry)可能導致 Secure Nested Paging(SNP)技術下的活躍虛擬中央處理器(vCPU)重複使用其他虛擬機器(VM)的 TLB 條目,進而可能危及資料完整性。AMD 針對此漏洞AMD 緩解措施。此漏洞影響Supermicro H12、H13 及H14 BIOS。
- CVE-2025-29934
Supermicro BMC 韌體漏洞,2025 年 10 月
在部分 Supermicro 主機板和 CMM 中已發現數個安全性問題。這些問題影響 Supermicro BMC 韌體。
- CVE-2025-7704
AMD 公告 AMD-SB-705AMD,2025 年 10 月
Supermicro 一項安全問題,該問題可能導致 RDSEED 指令以不符合隨機性的頻率返回「0」,同時錯誤地發出成功訊號(CF=1),這表示系統可能將失敗錯誤地判定為成功。AMD 針對此漏洞AMD 緩解措施。此漏洞影響Supermicro H13 H14 BIOS。
- CVE-2025-62626
AMD 公告 AMD-SB-302AMD,2025 年 10 月
Supermicro 一項安全問題,即惡意虛擬管理程式可能在「安全嵌套分頁 (SNP)」初始化過程中損毀反向映射表 (RMP)。此問題影響AMD EPYC™ 、4 及 5 代處理器。此漏洞影響Supermicro H12、H13 及H14 BIOS。
- CVE-2025-0033
Supermicro BMC 韌體漏洞,2025 年 9 月
在部分 Supermicro 主機板中已發現數個安全性問題。這些問題影響 Supermicro BMC 韌體。
- CVE-2025-7937
- CVE-2025-6198
英特爾平台更新 (IPU) 更新 2025.2 第二部分,2025年8月
此更新適用於搭載 IntelXeon® Intel 處理器的X11、X12、X13 及X14 。Intel 平台更新 (IPU) 整合了先前可能分別提供的各項安全性更新。
- INTEL-SA-01245– 2025.2 IPU - Intel® TDX 模組安全公告
- INTEL-SA-01249– 2025.2 IPU - Intel® 處理器流快取安全公告
英特爾平台更新 (IPU) 更新 2025.3,2025年8月
此更新適用於搭載 IntelXeon® Intel 處理器的X11、X12、X13 及X14 。Intel 平台更新 (IPU) 整合了先前可能分別提供的各項安全性更新。
- INTEL-SA-01280– 2025.3 IPU - Intel® 晶片組韌體安全公告
- INTEL-SA-01312– 2025.3 IPU - Intel® TDX 模組安全公告
- INTEL-SA-01313– 2025.3 IPU - Intel®Xeon® 韌體安全公告
AMD 漏洞,2025 年 8 月
此更新適用於搭載第一代/
- AMD–AMD 漏洞 – 2025 年 8 月
- AMD–AMD 漏洞 – 2025 年 2 月
AMD 公告AMD02AMD,2025 年 7 月
Supermicro AMD 瞬態執行安全漏洞。AMD 在調查微軟® 題為《進入、退出、頁錯誤、洩漏:測試微架構洩漏的隔離邊界》AMD 數種側通道攻擊。
- CVE-2024-36348
- CVE-2024-36349
- CVE-2024-36350
- CVE-2024-36357
2025.1 IPU - Intel® 處理器技術通告,INTEL-TA-01209,2025年6月
Supermicro 一項安全漏洞,即未經訓練的使用者若透過本地作業系統存取進行使用者驗證,可能利用 Intel® PTT 韌體中的 Intel® CSME 和 Intel® SPS 韌體進行越界讀取,藉此發動拒絕服務攻擊,進而影響系統可用性(高風險)。
- CVE-2025-2884
AMD 公告AMD-SB-7039,2025 年 6 月
Supermicro 一安全漏洞,該漏洞可能使具備特權的攻擊者透過 x86 架構存取加密協處理器 (CCP) 寄存器。此問題影響AMD EPYC™ 、2 及 3 代處理器,以及部分H11 H12 的產品。
- CVE-2023-20599
英特爾平台更新 (IPU) 更新 2025.2,2025年5月
此更新適用於搭載 IntelXeon® Intel 處理器的X11、X12、X13 及X14 。Intel 平台更新 (IPU) 整合了先前可能分別提供的各項安全性更新。
- INTEL-SA-01244– 2025.2 IPU - Intel® 處理器安全公告
- INTEL-SA-01247– 2025.2 IPU - Intel® 處理器間接分支預測器安全公告
2025.1 IPU - Intel® 處理器技術通告,INTEL-TA-01153,2025年5月
處理器事件或預測可能會導致錯誤的運算(或使用錯誤資料的正確運算)暫時執行,進而可能透過隱蔽通道洩露資料。間接分支預測可能無法完全受增強型 IBRS 屬性及間接分支預測器屏障所限制。此更新適用於搭載 IntelXeon® Intel 處理器的X11、X12 及X13 。
此漏洞影響Supermicro 部分H13 Supermicro 。Supermicro 任何關於本安全公告所述漏洞的公開通報,亦Supermicro 該漏洞遭惡意利用的案例。
- INTEL-SA-01153 – 2025.1 IPU - Intel® 處理器安全公告
AMI 安全公告 AMI-SA-2025003,2025年3月
Supermicro 已知悉 AMI 安全性公告 AMI-SA202503 中所報告的 BIOS 韌體潛在漏洞。Aptio® V 的 BIOS 存在漏洞,攻擊者可能透過本機方式造成「檢查時間與使用時間 (TOCTOU)」競爭條件。成功利用此漏洞可能導致任意程式碼執行。
此漏洞影響Supermicro 部分H13 Supermicro 。Supermicro 任何關於本安全公告所述漏洞的公開通報,亦Supermicro 該漏洞遭惡意利用的案例。
- CVE-2024-54084
AMD 公告AMD03AMD,2025 年 3 月
Supermicro Google® 所通報的安全問題,該問題稱為「AMD 驗證漏洞」,係因簽章驗證演算法存在弱點所致;此漏洞可能使具備管理員權限的攻擊者得以載入任意的CPU 修補程式。
- CVE-2024-36347
英特爾平台更新 (IPU) 更新 2025.1,2025年2月
此更新適用於搭載 IntelXeon® Intel 處理器的X11、X12 及X13 。Intel 平台更新 (IPU) 整合了先前可能分別提供的各項安全性更新。
- INTEL-SA-01139– 2025.1 IPU - UEFI 韌體安全公告
- INTEL-SA-01152– 2025.1 IPU - Intel® 晶片組韌體安全公告
- INTEL-SA-01213– 2025.1 IPU - Intel® SGX 安全公告
- INTEL-SA-01228– 2025.1 IPU - 第 13 代與第 14 代 Intel® Core™ 處理器安全公告
AMD 漏洞,2025 年 2 月
此更新適用於搭載第一代/
- AMD–AMD 漏洞 – 2025 年 2 月
- AMD–AMD 漏洞 – 2025 年 2 月
AMD 公告AMD,2025 年 2 月
Supermicro Eclypsium 所通報的系統管理模式 (SMM) 呼叫漏洞,該漏洞Supermicro 於多款AMD 所支援的 AmdPlatformRasSspSmm UEFI 模組中。此問題影響AMD EPYC™ 處理器,以及H11 H12 的產品。
- CVE-2024-21924
AMD 公告AMD,2025 年 2 月
Supermicro Quarkslab 所通報的兩項安全漏洞,這些漏洞存在於多款AMD 所支援的 AmdPspP2CmboxV2 及 AmdCpmDisplayFeatureSMM UEFI 模組中,可能使攻擊者在 SMM(系統管理模式)內執行程式碼。此問題影響AMD EPYC™ 、2、3 及 4 代處理器,以及H11、H12 和H13 的產品。
- CVE-2024-0179
- CVE-2024-21925
AMD 公告AMD,2025 年 2 月
Supermicro 電源管理韌體 (PMFW) 及AMD 單元 (SMU) 中的安全漏洞。此問題影響AMD H13 H13DSG-OM 產品。
- CVE-2024-21927
- CVE-2024-21935
- CVE-2024-21936
AMD 公告AMD,2025 年 2 月
Supermicro 電源管理韌體 (PMFW) 及AMD 單元 (SMU) 中的安全漏洞。此問題影響AMD H13 H13DSG-OM 產品。
- CVE-2024-21971
- CVE-2023-20508
AMD 公告AMD,2025 年 2 月
Supermicro 已知悉 Google® 所報告的安全性漏洞,其中具備管理員權限的攻擊者可能利用簽章驗證演算法中的弱點,並載入任意 CPU 微碼修補程式,這可能導致機密客體的 SEV 式保護遺失。
- CVE-2024-56161
Supermicro BMC IPMI 韌體漏洞,2025 年 1 月
在部分 Supermicro 主機板中已發現數個安全性問題。這些問題影響 Supermicro BMC 韌體。
- CVE-2024-10237
- CVE-2024-10238
- CVE-2024-10239
AMD 公告 AMD-SB-301AMD,2024 年 12 月
Supermicro 一項安全問題,該問題可能導致序列存在檢測 (SPD) 元資料遭到篡改,使連接的記憶體模組顯示容量大於實際容量,進而可能引發記憶體位址重疊。此問題影響搭載AMD EPYC™ 代及第 4 代處理器的主機板。此漏洞影響Supermicro H12 H13 BIOS。
- CVE-2024-21944
Supermicro BMC IPMI 韌體漏洞:「Terrapin」,2024 年 10 月
在部分 Supermicro 主機板中已發現一個安全性問題。Terrapin 漏洞允許攻擊者降級安全簽章演算法並停用特定的安全性措施。Terrapin 攻擊需要一個活躍的中間人攻擊者。
- CVE-2023-48795
BIOS 漏洞,2024年9月
Supermicro 已知悉 BIOS 韌體中的兩個潛在漏洞。這些漏洞可能允許攻擊者寫入 SMRAM 並劫持 RIP/EIP。它們影響 Denverton 平台中的 Supermicro BIOS。Supermicro 並未得知任何公開公告或惡意利用本公告所述之這些漏洞的案例。
- CVE-2020-8738
- CVE-2024-44075
英特爾平台更新 (IPU) 更新 2024.3,2024年8月
此更新適用於搭載 IntelXeon® Intel 處理器的X11、X12 及X13 。Intel 平台更新 (IPU) 整合了先前可能分別提供的各項安全性更新。
- INTEL-SA-01038– 2024.2 IPU - Intel® Core™Ultra 快取安全公告
- INTEL-SA-01046– 2024.2 IPU - Intel® 處理器流快取安全公告
- INTEL-SA-00999– 2024.3 IPU - Intel® 晶片組韌體安全公告
- INTEL-SA-01083– 2024.3 IPU - SMI 傳輸監控器安全公告
- INTEL-SA-01100– 2024.3 IPU - Intel®Xeon® 公告
- INTEL-SA-01118– 2024.3 IPU - 第三代 Intel®Xeon® 處理器安全公告
- INTEL-SA-01103– 2024.3 IPU - Intel® 處理器 RAPL 介面安全公告
AMD 漏洞,2024 年 8 月
此更新適用於搭載EPYC™ 1、2、3 或 4 代AMD EPYC™ H11、H12 H13 。此更新亦適用於搭載 Ryzen™ Threadripper™ 處理器的 M11、M12 及H13 。已發現各平台元件中潛在的漏洞,並已在AMD EPYC™ AMD AGESA™ PI 套件中進行了修復。
- AMD–AMD 漏洞 – 2024 年 8 月
- AMD–AMD 漏洞 – 2024 年 8 月
AMD 公告 AMD-SB-701AMD,2024 年 8 月
Supermicro 項安全漏洞,即即使啟用了 SMM Lock 功能,具備 root 權限的攻擊者仍可能修改系統管理模式 (SMM) 的設定。此問題影響AMD EPYC™ 、2、3 及 4 代處理器,以及H11、H12 和H13 。
- CVE-2023-31315
AMD 公告 AMD-SB-301AMD,2024 年 8 月
Supermicro 一項安全問題,即惡意虛擬化管理程式可能在 Secure Encrypted Virtualization–Secure Nested Paging (SEV-SNP) 客體虛擬機器停用後,解密其記憶體內容。此問題影響搭載AMD EPYC™ 代及第 4 代處理器的主機板。此漏洞影響Supermicro H12 H13 BIOS。
- CVE-2023-31355
- CVE-2024-21978
- CVE-2024-21980
PKFAIL:Supermicro BIOS 韌體漏洞,2024 年 7 月
Supermicro 已修復稱為「PKFAIL」的安全性漏洞問題。此新漏洞可能允許惡意行為者從作業系統發動進階韌體層級威脅。經確認,部分 Supermicro 產品使用了不安全的平台金鑰 (PK),這些金鑰代表 BIOS 的信任根。這些不安全的金鑰由 American Megatrends International (AMI) 生成,並作為參考範例提供給 Supermicro。
詳細資訊OpenSSH「regreSSHion」漏洞,2024年7月
在部分 Supermicro 主機板的 BMC 韌體中,發現了 OpenSSH 中一個關鍵訊號處理器競爭條件的安全漏洞,稱為「regreSSHion」。此漏洞可能導致未經身份驗證的遠端程式碼執行 (RCE),並具備 root 權限。
- CVE-2024-6387
BIOS 漏洞,2024年7月
Supermicro BIOS 韌體中存在潛在漏洞。這些漏洞影響部分X11 。Supermicro 任何關於本安全公告所述漏洞的公開通報,Supermicro 該等漏洞遭惡意利用的Supermicro 。
- CVE-2024-36432
- CVE-2024-36433
- CVE-2024-36434
Supermicro BMC IPMI 韌體漏洞,2024 年 7 月
在部分 Supermicro 主機板中發現了一個安全問題。此問題影響其 BMC 的網頁伺服器元件。Supermicro BMC 中的此潛在漏洞可能源於韌體中「GetValue」函數的緩衝區溢位,其原因是缺乏對輸入值的檢查。
- CVE-2024-36435
AMD 公告 AMD-SB-104AMD,2024 年 6 月
Supermicro AMD 保護功能中潛在的弱點。此問題影響搭載AMD EPYC™ 、2 及 3 代處理器的主機板。此漏洞影響Supermicro H11 H12 BIOS。
- CVE-2022-23829
AMD 公告AMD0AMD,2024 年 5 月
Supermicro AMD (驅動程式執行環境)驅動程式中存在記憶體洩漏漏洞,此漏洞可能存在於伺服器、客戶端桌面及行動 APU/CPU 中,並可能使具備高度權限的使用者取得敏感資訊。此問題影響AMD EPYC™ 處理器及主機板。此漏洞亦影響Supermicro H12 BIOS。
- CVE-2023-20594
- CVE-2023-20597
英特爾平台更新 (IPU) 更新 2024.2,2024年5月
此更新適用於搭載 IntelXeon® Intel 處理器的X13 。Intel 平台更新 (IPU) 整合了先前可能分別提供的各項安全性更新。
- INTEL-SA-01036– 2024.2 IPU - Intel® TDX 模組軟體安全公告
- INTEL-SA-01051– 2024.2 IPU - Intel® 處理器安全公告
- INTEL-SA-01052– 2024.2 IPU - Intel® Core™Ultra 公告
Supermicro BMC 韌體漏洞,2024 年 4 月
在部分 Supermicro 主機板中發現了數個安全漏洞。這些問題(跨站點腳本和命令注入)可能會影響 Supermicro BMC IPMI (Web UI) 的網頁伺服器元件。已發布更新的 BMC 韌體以緩解這些潛在漏洞。
- SMC-2024010010(CVE:CVE-2024-36430)
- SMC-2024010011(CVE:CVE-2024-36431)
- SMC-2024010012(CVE:CVE-2023-33413)
英特爾平台更新 (IPU) 更新 2024.1 與 INTEL-TA-00986,2024 年 3 月
此更新適用於搭載 IntelXeon® Intel 處理器的X11、X12 及X13 。Intel 平台更新 (IPU) 整合了先前可能分別提供的各項安全性更新。
- INTEL-SA-00898– 2024.1 IPU - Intel® Atom® 處理器安全公告
- INTEL-SA-00923– 2024.1 IPU - Intel® 晶片組軟體與 SPS 安全公告
- INTEL-SA-00929– 2024.1 IPU - 韌體建議公告
- INTEL-SA-00950– 2024.1 IPU OOB - Intel® 處理器安全公告
- INTEL-SA-00960– 2024.1 IPU - Intel®Xeon® 公告
- INTEL-SA-00972– 2024.1 IPU - Intel® 處理器匯流排鎖定安全公告
- INTEL-SA-00982– 2024.1 IPU - Intel® 處理器回溯預測安全公告
- INTEL-SA-00986– 第四代 Intel®Xeon® 安全公告
- INTEL-SA-01045– 2024.1 IPU OOB - Intel®Xeon® 處理器安全公告
AMD 公告 AMD-SB-700AMD,2024 年 2 月
Supermicro AMD 。此問題影響AMD AMD EPYC™ 代、EPYC™ 代、EPYC™ 代及第 4 代處理器。此漏洞影響Supermicro H11、H12 H13 。
- CVE-2023-20576
- CVE-2023-20577
- CVE-2023-20579
- CVE-2023-20587
AMD 公告 AMD-SB-300AMD,2024 年 2 月
Supermicro SEV-SNP 韌體漏洞。此問題影響AMD EPYC™ 代及第 4 代處理器。此漏洞影響Supermicro H12 部分H13 。
- CVE-2023-31346
- CVE-2023-31347
PixieFAIL 漏洞,2024年1月
Supermicro BIOS 韌體中存在一項名為「PixieFAIL」的潛在漏洞。研究人員在 Tianocore EDKII(一種 UEFI 的開源實作)的 TCP/IP 堆疊(NetworkPkg)中發現了多項漏洞。這九項漏洞若透過網路遭到利用,可能導致遠端程式碼執行、拒絕服務(DoS)攻擊、DNS 快取中毒,以及/或敏感資訊外洩。 PixieFAIL 影響Supermicro 特定X11、X12、H11、H12、H13 R12 產品的Supermicro 。Supermicro 任何關於本安全公告所述漏洞的公開通報,Supermicro 相關漏洞遭惡意利用的Supermicro 。
- CVE-2023-45229
- CVE-2023-45230
- CVE-2023-45231
- CVE-2023-45232
- CVE-2023-45233
- CVE-2023-45234
- CVE-2023-45235
- CVE-2023-45236
- CVE-2023-45237
LogoFAIL 漏洞,2023年12月
Supermicro BIOS 韌體中存在一項名為「LogoFAIL」的潛在漏洞。 BIOS 所使用的圖像解析函式庫中,若輸入驗證機制不完善,可能導致具特權的使用者透過本地存取來提升權限。LogoFAIL 影響Supermicro 特定X11、X12、X13、H11、M12 及 R12 產品的Supermicro 。Supermicro 任何關於本安全公告所述漏洞的公開通報,Supermicro 相關漏洞遭惡意利用的Supermicro 。
- CVE-2023-39538
- CVE-2023-39539
Supermicro BMC IPMI 韌體中的漏洞,2023 年 12 月
- CVE-2023-33411:IPMI BMC SSDP/UPnP 網頁伺服器目錄遍歷漏洞及 iKVM 存取權限,允許重新啟動 BIOS
- CVE-2023-33412:IPMI BMC 管理網頁介面虛擬軟碟機/USB 遠端指令執行漏洞
- CVE-2023-33413:IPMI BMC 裝置使用硬編碼的配置檔案加密金鑰,允許攻擊者構建並上傳惡意配置檔案套件,從而取得遠端指令執行權限。
AMD 公告AMD
Supermicro AMD 指令的安全漏洞。此問題影響第一代AMD EPYC™ (SEV 和 SEV-ES)、第二代AMD EPYC™ (SEV 和 SEV-ES),以及第三代AMD EPYC™ (SEV、SEV-ES、SEV-SNP)。 此漏洞影響Supermicro H11 H12 。
- CVE-2023-20592
英特爾平台更新 (IPU) 更新 2023.4 與 INTEL-SA-00950,2023 年 11 月
此更新適用於搭載 IntelXeon® Intel 處理器的X11、X12 及X13 。Intel 平台更新 (IPU) 整合了先前可能分別提供的各項安全性更新。
- INTEL-SA-00924– 2023.4 IPU – 基本輸入輸出系統(BIOS)安全公告
- INTEL-SA-00950– Intel® 處理器安全公告
AMD 漏洞,2023 年 11 月
此更新適用於搭載第一代/
- AMD-AMD 漏洞 – 2023 年 11 月
- AMD-AMD 漏洞 – 2023 年 11 月
Supermicro BMC IPMI 韌體中的漏洞
在部分 Supermicro 主機板中發現了數個安全漏洞。這些問題(跨站點腳本和命令注入)可能會影響 Supermicro BMC IPMI (Web UI) 的網頁伺服器元件。已發布更新的 BMC 韌體以緩解這些潛在漏洞。
- CVE-2023-40289
- CVE-2023-40284
- CVE-2023-40287
- CVE-2023-40288
- CVE-2023-40290
- CVE-2023-40285
- CVE-2023-40286
因堆疊溢位導致的變數修改
在 Supermicro BIOS 韌體中發現了一個潛在漏洞。攻擊者可以透過操縱變數來利用 Supermicro 主機板中的此漏洞,潛在地劫持控制流,允許具有核心層級權限的攻擊者提升其權限並潛在地執行任意程式碼。
- CVE-2023-34853
AMD 公告AMD
Supermicro 「回送位址預測器」(Return Address Predictor)漏洞,此漏洞亦稱為「INCEPTION」。此漏洞影響AMD EPYC™ 代及第 4 代處理器。此漏洞影響Supermicro H12 部分H13 。
- CVE-2023-20569
英特爾平台更新 (IPU) 更新 2023.3,2023年8月
此更新適用於搭載 IntelXeon® Intel 處理器的X11、X12 及X13 。Intel 平台更新 (IPU) 整合了先前可能分別提供的各項安全性更新。
- INTEL-SA-00783– 2023.2 IPU – Intel® 晶片組韌體安全公告
- INTEL-SA-00813– 2023.2 IPU – 韌體公告
- INTEL-SA-00828– 2023.2 IPU – Intel® 處理器安全公告
- INTEL-SA-00836– 2023.2 IPU – Intel®Xeon® 處理器安全公告
- INTEL-SA-00837– 2023.2 IPU – Intel®Xeon® 公告
AMD 公告AMD
Supermicro 跨進程資訊外洩問題,亦稱為「Zenbleed」。此問題影響AMD EPYC™ 處理器,亦即AMD 2」處理器。此漏洞影響Supermicro H11 H12 。
- CVE-2023-20593
SMTP 通知中的 Shell 注入
特定 Supermicro 主機板中的漏洞可能會影響 SMTP 通知配置。此漏洞可能允許未經身份驗證的惡意行為者控制使用者輸入,例如警報設定中的主旨,這可能導致任意程式碼執行。
- CVE-2023-35861
服務定位協議(SLP)中的反射式拒絕服務(DoS)放大漏洞
服務位置協定(SLP)允許未經認證的遠端攻擊者註冊任意服務。此漏洞可能使攻擊者得以利用偽造的UDP流量發動具有顯著放大效果的拒絕服務(DoS)攻擊。
- CVE-2023-29552
媒體資訊:英特爾 BootGuard OEM 私有金鑰可能已遭洩露,2023年5月
根據對 Supermicro 如何產生和使用私密金鑰的分析,Supermicro 產品不受影響。
英特爾平台更新 (IPU) 更新 2023.2,2023年5月
此更新適用於搭載 IntelXeon® Intel 處理器的X11、X12 及X13 。Intel 平台更新 (IPU) 整合了先前可能分別提供的各項安全性更新。
- INTEL-SA-00807– 2023.2 IPU – BIOS 安全公告
AMD 漏洞,2023 年 5 月
此更新適用於搭載第一代、第二代、第三代及第四代AMD EPYC™ H11、H12 H13 。此更新亦適用於搭載 Ryzen™ Threadripper™ 處理器的 M12 產品系列。已發現各平台元件中潛在的漏洞,並已在AMD EPYC™ AMD AGESA™ PI 套件中進行了修復。
- AMD-AMD 漏洞 – 2023 年 5 月
- AMD-AMD 漏洞 – 2023 年 5 月
超級醫生5諮詢報告,2023年3月
研究人員已發現 Supermicro SuperDoctor5 (SD5) 中的一個漏洞,該漏洞可能允許網頁介面上的任何已驗證使用者在安裝 SuperDoctor5 (SD5) 的系統上遠端執行任意指令。
- CVE-2023-26795
英特爾平台更新 (IPU) 更新 2023.1,2023 年 2 月
此更新適用於搭載 IntelXeon® Intel 處理器的X11、X12 及X13 。Intel 平台更新 (IPU) 整合了先前可能分別提供的各項安全性更新。
- INTEL-SA-00700– 2023.1 IPU – Intel® Atom® 及 Intel®Xeon® 處理器安全公告
- INTEL-SA-00717– 2023.1 IPU – BIOS 安全公告
- INTEL-SA-00718– 2023.1 IPU – Intel® 晶片組韌體安全公告
- INTEL-SA-00730– 2023.1 IPU – 第三代 Intel®Xeon® 處理器安全公告
- INTEL-SA-00738– 2023.1 IPU – Intel®Xeon® 公告
- INTEL-SA-00767– 2023.1 IPU – Intel® 處理器安全公告
電壓調節器模組(VRM)與集成電路間(I²C)過壓/欠壓問題,2023年1月
研究人員發現主機板管理控制器(BMC)存在一項漏洞,可能導致電壓調整超出CPU )的指定運作CPU 正常CPU 。
- CVE-2022-43309
AMD 漏洞,2023 年 1 月
此更新適用於搭載第一代、第二代、第三代及第四代AMD EPYC™ H11 H12 。此更新亦適用於搭載 Ryzen™ Threadripper™ 處理器的 M12 產品系列。已發現各平台元件中存在潛在漏洞,並已在AMD EPYC™ AMD AGESA™ PI 套件中進行了修復。
- AMD-AMD 漏洞 – 2023 年 1 月
- AMD-AMD 漏洞 – 2023 年 1 月
英特爾平台更新 (IPU) 更新 2022.3,2022 年 11 月
此更新適用於搭載 IntelXeon® Intel 處理器的X11 及X12 。Intel 平台更新 (IPU) 整合了先前可能分別提供的各項安全性更新。
- INTEL-SA-00610- 2022.3 IPU – Intel® 晶片組韌體安全公告
- INTEL-SA-00668- 2022.2 IPU – BIOS 安全公告
OpenSSL 安全公告,2022年11月
OpenSSL 3.x 至 3.0.6 版本被發現存在一個高嚴重性安全漏洞,可能導致系統崩潰或意外行為。Supermicro 產品不受此 OpenSSL 漏洞影響。
- CVE-2022-3786
- CVE-2022-3602
Microsoft Windows 啟動繞過漏洞,2022 年 8 月
研究人員Microsoft第三方開機載入程式中發現數個漏洞,這些漏洞可能影響所有使用 x64 UEFI 安全開機的電腦系統。
- CVE-2022-34301
- CVE-2022-34302
- CVE-2022-34303
英特爾平台更新 (IPU) 更新 2022.2,2022年8月
此更新適用於搭載 IntelXeon® Intel 處理器的X11 及X12 。Intel 平台更新 (IPU) 整合了先前可能分別提供的各項安全性更新。
- INTEL-SA-00657- 2022.2 IPU – Intel® 處理器安全公告
- INTEL-SA-00669- 2022.2 IPU – Intel® 晶片組韌體安全公告
- INTEL-SA-00686- 2022.2 IPU – BIOS 安全公告
英特爾平台更新 (IPU) 更新 2022.1,2022年6月
此更新適用於搭載 IntelXeon® Intel 處理器的 X10、X11 及X12 。Intel 平台更新 (IPU) 整合了先前可能分別提供的各項安全性更新。
- INTEL-SA-00601- 2022.1 IPU – 基本輸入輸出系統(BIOS)安全公告
- INTEL-SA-00613- 2022.1 IPU – Intel® Boot Guard 與 Intel® TXT 安全公告
- INTEL-SA-00614- 2022.1 IPU – Intel® SGX 安全公告
- INTEL-SA-00615- 2022.1 IPU – Intel® 處理器 MMIO 過期資料安全公告
- INTEL-SA-00616- 2022.1 IPU – Intel®Xeon
- INTEL-SA-00617- 2022.1 IPU – Intel® 處理器安全公告
AMD 漏洞,2022 年 5 月
此更新適用於搭載第一代、第二代或第三代AMD EPYC™ H11 H12 。此更新亦適用於搭載 Ryzen™ Threadripper™ 處理器的 M12 產品系列。已發現各平台元件中潛在的漏洞,並已在AMD EPYC™ AMD AGESA™ PI 套件中進行了修復。
- AMD-AMD 漏洞 – 2022 年 5 月
- AMD-AMD 漏洞 – 2022 年 5 月
英特爾平台更新 (IPU) 更新 2021.2,2022年2月
此更新適用於搭載 IntelXeon® Intel 處理器的 X10、X11 及X12 。Intel 平台更新 (IPU) 整合了先前可能分別提供的各項安全性更新。
- INTEL-SA-00470- 2021.2 IPU – Intel® 晶片組韌體公告
- INTEL-SA-00527- 2021.2 IPU – BIOS 安全公告
- INTEL-SA-00532- 2021.2 IPU – Intel® 處理器中斷點控制流安全公告
- INTEL-SA-00561- 2021.2 IPU – Intel® 處理器安全公告
- INTEL-SA-00589- 2021.2 IPU – 英特爾凌動®處理器安全公告
Supermicro 對於 Apache Log4j 漏洞的回應
Supermicro 已知悉並與業界合作,以減輕由高優先級的 CVE-2021-44228 (Apache Log4j 2) 問題 (亦稱為「Log4Shell」)、CVE-2021-45046 (Apache Log4j 2) 問題,以及 CVE-2021-45105 (Apache Log4j 2) 問題所造成的風險。Supermicro 亦已知悉 Apache Log4j 1.2 的 CVE-2021-4104 和 CVE-2019-17571 問題。
大多數 Supermicro 應用程式不受這五個漏洞影響。唯一受影響的應用程式是 Supermicro Power Manager (SPM)。此問題將在 Supermicro Power Manager (SPM) 的新版本中解決,並將盡快發布。SPM 將隨附 Log4j 2.17.0 版。
Log4j 2
- CVE-2021-44228
- CVE-2021-45046
- CVE-2021-45105
Log4j 1.2
- CVE-2019-17571
- CVE-2021-4104
英特爾平台更新 (IPU) 更新 2021.2,2021年11月
此更新適用於搭載 IntelXeon® Intel 處理器的 X10、X11 及X12 。Intel 平台更新 (IPU) 整合了先前可能分別提供的各項安全性更新。
- INTEL-SA-00528- 2021.2 IPU – Intel® Atom® 處理器安全公告
- INTEL-SA-00562- 2021.1 IPU – BIOS 參考程式碼公告
AMD 漏洞,2021 年 11 月
此更新適用於搭載第一代、第二代或第三代AMD EPYC™ H11 H12 。已發現各平台元件中存在潛在漏洞,並已在AMD EPYC™ PI 套件中進行了修復。
- AMD-AMD 漏洞 – 2021 年 11 月
英特爾安全公告 Intel-SA-00525,2021年7月
- INTEL-SA-00525– 英特爾 BSSA(BIOS 共享軟體架構)DFT 諮詢公告
Intel-SA-00525 安全性公告不影響 Supermicro BIOS。
詳細資訊英特爾平台更新 (IPU) 更新 2021.1,2021 年 6 月
此更新適用於搭載 IntelXeon® Intel 處理器的 X10、X11 及X12 。Intel 平台更新 (IPU) 整合了先前可能分別提供的各項安全性更新。
- INTEL-SA-00442- 2021.1 IPU – Intel VT-d 安全公告
- 英特爾安全公告 - 00459- 2021.1 IPU – 英特爾安全公告 - CSME-SPS-TXE-DAL-AMT-安全公告
- INTEL-SA-00463- 2021.1 IPU – BIOS 安全公告
- INTEL-SA-00464- 2021.1 IPU – 英特爾處理器安全公告
- INTEL-SA-00465- 2021.1 IPU – 英特爾處理器安全公告
Supermicro 對於 Trickboot 漏洞的回應,2021 年 3 月
Supermicro 已知悉 Trickboot 問題,此問題僅在部分 X10 UP 主機板上觀察到。Supermicro 將針對此漏洞提供緩解措施。
TrickBoot 是TrickBot惡意軟體工具組中的一項新功能,能夠偵測裝置漏洞,並使攻擊者得以讀取、寫入或清除裝置的 BIOS。
閱讀更多BIOS 偵測到Linux 中的 GRUB2 開機載入器漏洞,2020 年 11 月
在 GRUB2 2.06 版本之前的版本中發現一項缺陷。攻擊者可能利用此缺陷劫持並竄改 GRUB 驗證程序。BIOS 將偵測到此異常狀態,並以錯誤訊息終止開機程序。
- CVE-2020-10713
英特爾平台更新 (IPU) 更新 2020.2,2020年11月
此更新適用於搭載 IntelXeon® Intel 處理器的 X10、X11 及X12 。Intel 平台更新 (IPU) 整合了先前可能分別提供的各項安全性更新。
- INTEL-SA-00358– 2020.2 IPU – 韌體建議公告
- INTEL-SA-00391– 2020.2 IPU – Intel® CSME、SPS、TXE 及 AMT 安全公告
- INTEL-SA-00389– 2020.2 IPU – Intel® RAPL 安全公告
- INTEL-SA-00390– 英特爾 BIOS 平台範例程式碼安全公告
英特爾每月安全更新(2020年9月)
此更新適用於搭載 Intel Core® 處理器的X11 X12 。Intel 9 月每月安全性更新整合了先前可能已分別發布的安全性更新。
請注意,X10 系列產品不受此公告影響。
- Intel-SA-00404– Intel® AMT 與 Intel® ISM 安全公告
英特爾平台更新 (IPU) 更新 2020.1,2020年6月
此更新適用於搭載 IntelXeon® X10 及X11 。Intel 平台更新 (IPU) 整合了先前可能已分別提供的各項安全性更新。
- Intel-SA-00295– Intel® CSME、SPS、TXE、AMT 及 DAL 安全公告
- Intel-SA-00320– 特殊登錄器緩衝區資料採樣公告
- Intel-SA-00322– 2020.1 IPU 韌體公告
- Intel-SA-00329– Intel® 處理器資料外洩安全公告
- Intel-SA-00260– (更新版) Intel® 處理器顯示卡 2019.2 QSR 更新公告
ErP(環保設計)合規第9批次
Lot 9規範是一套針對資料儲存設備(例如企業級伺服器)所制定的全新產品標準。了解Supermicro如何符合歐盟(EU)針對伺服器與儲存產品所制定的生態設計要求,實現Lot 9的合規性。
詳細資訊英特爾每月安全更新(2020年2月)
此更新適用於搭載 Intel Core® 處理器的X11 。Intel 2 月每月安全性更新整合了先前可能已分別發布的安全性更新。
- Intel-SA-00307– 權限提升、服務阻斷、資訊外洩
英特爾每月安全更新(十二月版),2019年12月
此更新適用於搭載 IntelXeon® X10 及X11 。Intel 12 月每月安全性更新整合了先前可能已分別發布的安全性更新。
- Intel-SA-00289– Intel® 處理器電壓設定變更建議
- Intel-SA-00317– 虛擬化環境中發生意外頁面錯誤安全公告
英特爾平台更新 (IPU) 更新 2019.2,2019年11月
此更新適用於搭載 IntelXeon® X10 及X11 。Intel 平台更新 (IPU) 整合了先前可能分別提供的各項安全性更新。
- Intel-SA-00164– Intel® 可信執行技術 2019.2 IPU 安全公告
- Intel-SA-00219– Intel® SGX 2019.2 搭配 Intel® 處理器圖形 IPU 更新建議
- Intel-SA-00220– Intel® SGX 與 Intel® TXT 安全公告
- Intel-SA-00240– 英特爾CPU 公告
- Intel-SA-00241– Intel® CSME、伺服器平台服務、可信執行引擎、Intel® 主動管理技術及 Dynamic Application Loader 2019.2 IPU 安全公告
- Intel-SA-00254– Intel® 系統管理模式 2019.2 IPU 安全公告
- Intel-SA-00260– Intel® 處理器圖形 2019.2 IPU 安全公告
- Intel-SA-00270– TSX 交易非同步中止安全公告
- Intel-SA-00271– 電壓調變技術諮詢公告
- Intel-SA-00280– BIOS 2019.2 IPU 安全公告
BMC/IPMI 安全性漏洞更新2019年9月3日
研究人員已發現 Supermicro BMC 虛擬媒體功能上的數個安全性相關問題,需要透過 BMC 韌體更新來解決。
CVE-2019-16649
CVE-2019-16650
英特爾季度安全更新 (QSR) 2019.1 版,2019年5月
此更新適用於搭載 IntelXeon® X8、X9、X10 及X11 。季度安全更新 (QSR) 整合了先前可能已分別發布的安全更新。
- 英特爾安全公告 00213(CVE-2019-0089, CVE-2019-0090, CVE-2019-0086, CVE-2019-0091, CVE-2019-0092, CVE-2019-0093, CVE-2019-0094、CVE-2019-0096、CVE-2019-0097、CVE-2019-0098、CVE-2019-0099、CVE-2019-0153、CVE-2019-0170)
- INTEL-SA-00223BIOS 未受影響
- 英特爾安全公告-00233(CVE-2018-12126、CVE-2018-12127、CVE-2018-12130、CVE-2019-11091)
針對這些問題的 BIOS 更新現正陸續推出。請參閱下方受影響產品及必要 BIOS 更新的詳細資訊。
英特爾季度安全更新 (QSR) 2018.4 版更新,2019年3月
此更新僅適用於搭載 IntelXeon® X11 。季度安全更新 (QSR) 整合了先前可能已分別發布的安全更新。
- 英特爾安全公告 00185(CVE-2018-12188, CVE-2018-12189, CVE-2018-12190, CVE-2018-12191, CVE-2018-12192, CVE-2018-12199, CVE-2018-12198、CVE-2018-12200、CVE-2018-12187、CVE-2018-12196、CVE-2018-12185、CVE-2018-12208)
- INTEL-SA-00191(CVE-2018-12201、CVE-2018-12202、CVE-2018-12203、CVE-2018-12205、CVE-2018-12204)
「劇透」:關於英特爾處理器投機執行的新研究論文
詳細資訊幽靈與熔毀側通道投機執行
- 英特爾 SA-00115(CVE-2018-3639, CVE-2018-3640)
- Intel-SA-00088(CVE-2017-5715, CVE-2017-5753, CVE-2017-5754)
- Intel-SA-00161(CVE-2018-3615, CVE-2018-3620, CVE-2018-3646)
有關 Intel® 管理引擎 (ME)、Intel® 伺服器平台服務 (SPS) 及 Intel® 可信執行引擎 (TXE) 的 Intel 安全漏洞
- Intel-SA-00086(CVE-2017-5705, CVE-2017-5708, CVE-2017-5711, CVE-2017-5712, CVE-2017-5706, CVE-2017-5709、CVE-2017-5707、CVE-2017-571000)
2017年之前的BIOS/BMC韌體安全性更新
請參閱2017年之前發布的《固件修復常見漏洞與暴露》文件。
Supermicro 積極與安全性社群合作,以識別並強化我們產品線的安全性。請查閱 Supermicro 韌體上發布的 CVE 解決方案。
詳細資訊常見安全問題集:選擇類別「安全」
回報產品安全問題
如果您遇到 Supermicro 產品的安全問題,請將電子郵件寄送至 secure@supermicro.com,並提供以下詳細資訊:
- 產品名稱/SKU
- 漏洞詳細報告
- 重現步驟說明
- 任何相關的CVE
請勿在明文電子郵件中包含任何敏感或機密資訊 – 請使用 PGP 金鑰加密您的訊息。Supermicro 產品安全團隊將審閱您的報告,並與您聯繫以共同解決問題。
詳細資訊獲取 Supermicro 的產品安全更新
立即訂閱
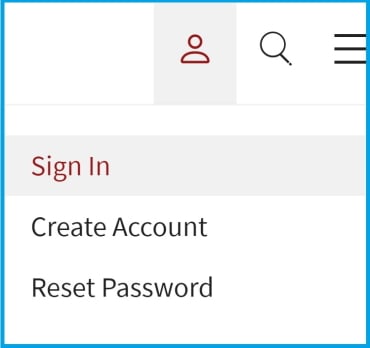
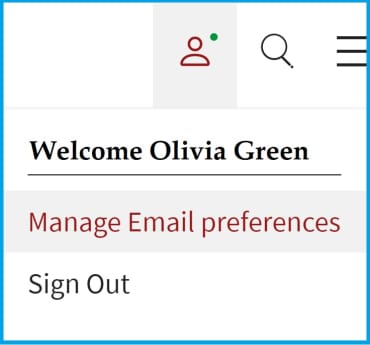
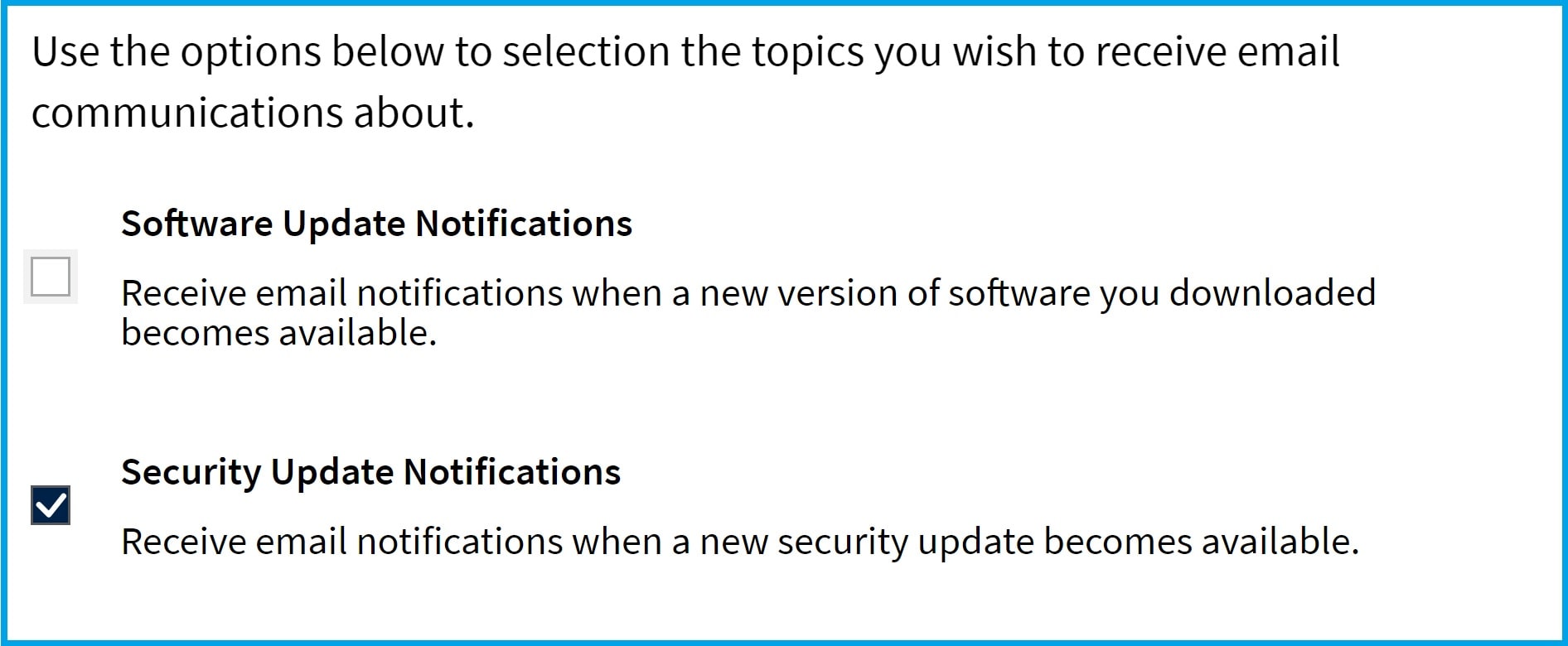
若要訂閱以接收未來的 Supermicro 安全警報,請依照以下步驟操作:
1. 請前往螢幕右上角區域,登入或建立單一登入(SSO)帳戶:
2. 選擇「管理電子郵件偏好設定」
3.勾選「安全性更新通知」
- 生效日期
- 最後更新
概述
在 Supermicro,我們致力於維護產品和服務的安全與完整性。本產品生命週期結束 (EOL) 安全政策概述了我們如何管理已達到 EOL 狀態產品的安全問題,以確保透明度並協助客戶規劃升級和轉換。
何謂產品終止(EOL)?
當我們正式宣布某項產品或服務將不再進行積極開發、維護或增強時,即視為該產品或服務已終止生命週期。
安全支援時程表
我們理解從舊有產品過渡需要時間。為支援我們的客戶:
- 嚴重性為「關鍵級」(9.0 - 10.0) 與「高風險級」(7.0 - 8.9) 的安全問題,將於產品生命週期終止公告日之後,持續獲得三年(3)年的支援服務。
- 在此期間,我們將評估所通報的漏洞,並可能根據嚴重程度與影響範圍發布修補程式或緩解措施。
- 三年期限屆滿後,將不再提供任何安全性更新或調查服務。
例外情況
超過標準三年期的延伸安全支援可能需透過單獨協議提供。請聯繫 Supermicro 討論相關選項。
聯繫我們
如對本政策有任何疑問或疑慮,請聯繫我們的安全團隊:secure@supermicro.com